This is a list, in no particular order, of principles to adhere when running a secure Linux server.
- SSH – Never allow direct SSH root access (set PermitRootLogin No).
- SSH – Do not use SSH keys without a passphrase.
- SSH – If possible, do not run SSH on a public IP interface (preferably use a management VLAN).
- SSH/SSL – Use strong SSH ciphers and MAC algorithms (Check with https://testssl.sh/).
- Never run anything as root (use sudo).
- Use deny all, allow only firewall principle. Block everything by default, only open what’s needed.
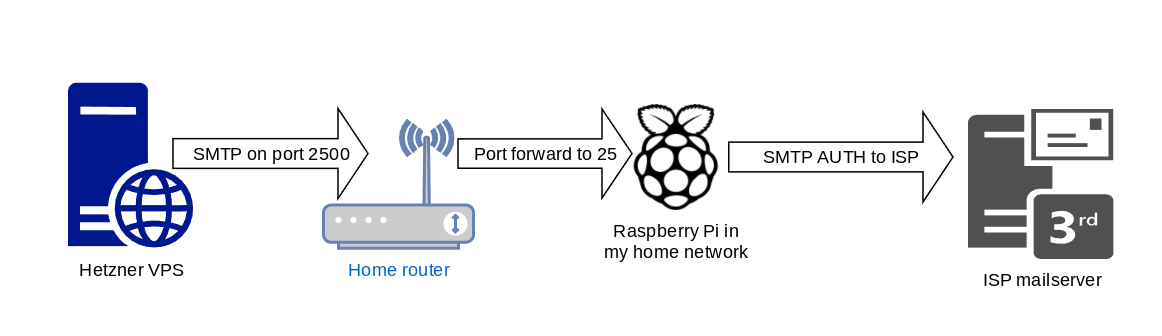
- Configure the mail daemon to use a smarthost (unless it’s a mailserver).
- Always use a timeserver daemon to keep server in sync (ntp).
- Always use a package manager and apply, at least once a month, updates (apt, yum etc.)
- Have backups in place and regularly test the restores.
- Do not just backup raw database data. Dump databases and backup those dumps (mysqldump, pg_dump).